Cryptocurrencies are digital coins secured by cryptography and primarily used for online purchases. They emerged as a byproduct of the groundbreaking digital cash system known as blockchain technology.
In the late 90s, the prospects for the development of a functional e-market were pretty bleak, especially after a couple of promising startups turned into failures – take what happened to DigiCash for example. Finally, with the blockchain breakthrough and the appearance of cryptocurrencies, the inconceivable dream of a decentralized yet trustworthy online market became a (virtual) reality.
Cryptocurrencies have always had their advocates and critics, with opinions ranging from “cryptos are the greatest invention ever” to “they’re the biggest market mirage in history”.
But before taking a stance on digital coins yourself, take your time to read through our detailed guide on cryptocurrencies.
We’ll dive into the history and the main incentives for creating these coins. We’ll talk about their attractiveness and sustainability, why there’s a growing number of unique cryptos, how and where to use them, and what are some of the benefits for the global economic system.
For those looking to dive into this world, we recommend checking out our best crypto exchanges in Australia list to start your journey with crypto.
Getting Started with Crypto
What is Cryptocurrency?
Cryptocurrencies are digital coins secured by cryptography and primarily used for online purchases. They emerged as a byproduct of the groundbreaking digital cash system known as blockchain technology.
In the late 90s, the prospects for the development of a functional e-market were pretty bleak, especially after a couple of promising startups turned into failures – take what happened to DigiCash for example. Finally, with the blockchain breakthrough and the appearance of cryptocurrencies, the inconceivable dream of a decentralized yet trustworthy online market became a (virtual) reality.
Cryptocurrencies have always had their advocates and critics, with opinions ranging from “cryptos are the greatest invention ever” to “they’re the biggest market mirage in history”.
But before taking a stance on digital coins yourself, take your time to read through our detailed guide on cryptocurrencies.
We’ll dive into the history and the main incentives for creating these coins. We’ll talk about their attractiveness and sustainability, why there’s a growing number of unique cryptos, how and where to use them, and what are some of the benefits for the global economic system.
So, without further ado, let’s dive in.
Cryptocurrencies Explained
If cryptocurrencies have caught your attention, you probably want to know what’s so exceptional about them.
The key to their revolutionary nature can be found in the way they make use of the main blockchain principles: decentralization, privacy, trust, and immutability.
The Story Behind Blockchains
Before we go into further details, you need to get acquainted with the main idea behind blockchain technology. Invented in 2008 by Satoshi Nakamoto, an individual whose true identity remains a secret. A blockchain is a digital ledger for storing information on a decentralized peer-to-peer network, based on crypto proof instead of trust.
Back in those days, trust-based payment systems were the norm. The traditional financial system allowed people to send money to friends and family, trade stock, and take out loans. At the same time, it came at a great cost, and not only literally. Apart from high transaction fees, this system compromised user privacy, took a lot of time for the transactions to be completed, especially if the transfer was international, and it wasn’t available to everyone.
The great stock market crash in 2008 was like the explosion of a ticking time bomb. People lost faith and trust in financial institutions, and their disapproval was even greater when the state had to bail out many banks and investors using tax money. It was also an additional incentive for cryptographers like Satoshi to come up with an alternative payment system.
And this is exactly what they did. For the first time ever, they proposed a completely devised non-trust based system, detailed in the Bitcoin white paper.
What Lies Beyond Trust?
In 2009, on the P2P Foundation website, a discussion under the name Bitcoin open source implementation of P2P currency opened by Satoshi Nakamoto stated the following:
The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve. We have to trust them with our privacy, trust them not to let identity thieves drain our accounts. Their massive overhead costs make micropayments impossible.
Cryptocurrencies have managed to vault over these limitations and inconveniences, and exist independently from any third party. They’re immune to government meddlings and trust-based models of exchange that make us compromise our privacy. On top of that, they’re very cost-effective, even as far as micropayments go, since there are no intermediaries to set those audacious processing fees we are accustomed to.
What’s a “Good” Currency?
For cryptocurrencies to be accepted and widely used, they have to meet certain currency criteria. As you already know, a currency is a monetary unit that denominates cash flows, and you can either invest them or use their purchasing power.
On their own, currencies can’t be valued since they’re without cash flows but they can be priced against other currencies. The purchasing or buying power of a currency can vary due to inflation, deflation, and other economic phenomena, regulated by the government with different policies such as interest rates, quantitative easing, etc.
To measure a currency’s standing, you should take into account how it delivers on the following purposes:
Unit of account
The first purpose of a currency is to serve as a unit of account or a measurement of value. You can value goods, services, assets, labor, income, expenses, and liabilities. This allows us to evaluate anything we produce or consume and compare it in monetary values based on different currencies such as the US dollar or the Euro. To perform the role of a unit of account effectively, a currency has to be fungible, divisible, and countable.
Medium of exchange
The second function of a currency is to intermediate the exchange of goods and services, i.e. to be accepted as a payment method in a transaction or for the repayment of debts. This is only possible if buyers and sellers recognize and later on trust the value of that particular currency, and if transaction costs are affordable. A currency will be an even better candidate if it’s easily accessible and portable.
Store of value.
A currency is considered to be a store of value if it retains its purchasing power in the long run. This means that if you hold on to this currency or make investments with it, you’ll still profit in the future. You’ll be able to save, retrieve, and exchange the currency later on without being at a loss.
What Makes Cryptocurrency a Currency?
Before we answer the question, let’s classify the existent types of money to get a better idea of how cryptocurrencies differ from traditional fiat currencies. This classification, included in a 2018 monetary dialogue made at the request of the European Parliament Committee on Economic and Monetary Affairs, focuses on three criteria among those discussed by Bech and Garratt (2017): a) issuer: government or private; b) form: physical or digital; and c) how transactions are settled: centralized or decentralized.

Fiat currencies have the advantage of being backed by the government, they’re tangible objects, and they’re regulated by intermediaries. On the other hand, there are cases where they became almost worthless in the event of hyperinflation. These cases are rare, but the risk still exists. What’s the status of the cryptocurrencies? We see that they’re private, digital, and decentralized. But how well do they deliver on the above-mentioned currency purposes?
Cryptocurrencies function seamlessly as units of account since they’re fungible, divisible, and countable.
In economics, a fungible currency is when two separate units of a particular currency have the same value and can be exchanged at the same rate. One Bitcoin values the same as another Bitcoin. Next, cryptocurrencies are even more divisible than fiat currencies. One Satoshi is a hundredth of a millionth of Bitcoin or, for example, if a Bitcoin is worth $100,000, one Satoshi would be worth $0.0010.
In the beginning, digital coins weren’t the best mediums of exchanges or stores of value, since most merchants were skeptical and didn’t want to risk accepting them as payment methods. Even if they did, like Overstock in 2014, they did so on limited items only and partnered with a third-party that would convert cryptos to fiat currencies for them. Luckily, things have started changing in the past couple of years.
The History of Cryptocurrencies
Cryptocurrency is such a powerful concept that it can almost overturn governments. – Charles Lee, Litecoin founder
Satoshi Nakamoto might have been the one credited for the creation of blockchain but his idea was inspired by previous projects and innovations. Ten years prior to his white paper, which described how he envisioned the blockchain to function, another famous cryptographer Wei Dai proposed his own idea of digital money called B-Money.
His idea, much like Satoshi’s, was to make sure customers can pay anonymously with digital money using digital pseudonyms. Dai discussed two protocols that the network could implement to verify online transactions but he couldn’t solve the double-spend problem completely. Satoshi was the first one who overcame this obstacle in a decentralized cash system.
In the famous White Paper, Satoshi used the term ‘Bitcoin’ to refer to the whole peer-to-peer electronic cash payment system that he had been working on for over a year. The term ‘blockchain’ came a bit later, and it stands for the core elements of the technology: the data stored on the digital ledger (e.g. the transactions) is stored in “blocks” which are then “chained” together in succession by means of a hash function.
Bitcoin
On January 3rd 2009, Satoshi Nakamoto mined the first Bitcoin block (Block 0) on the blockchain network, the prototype of all blocks to follow, piloting his electronic cash system. This block became known as the Genesis Block.
The block had the following message:
The Times 03/Jan/2009 Chancellor on brink of second bailout for banks.
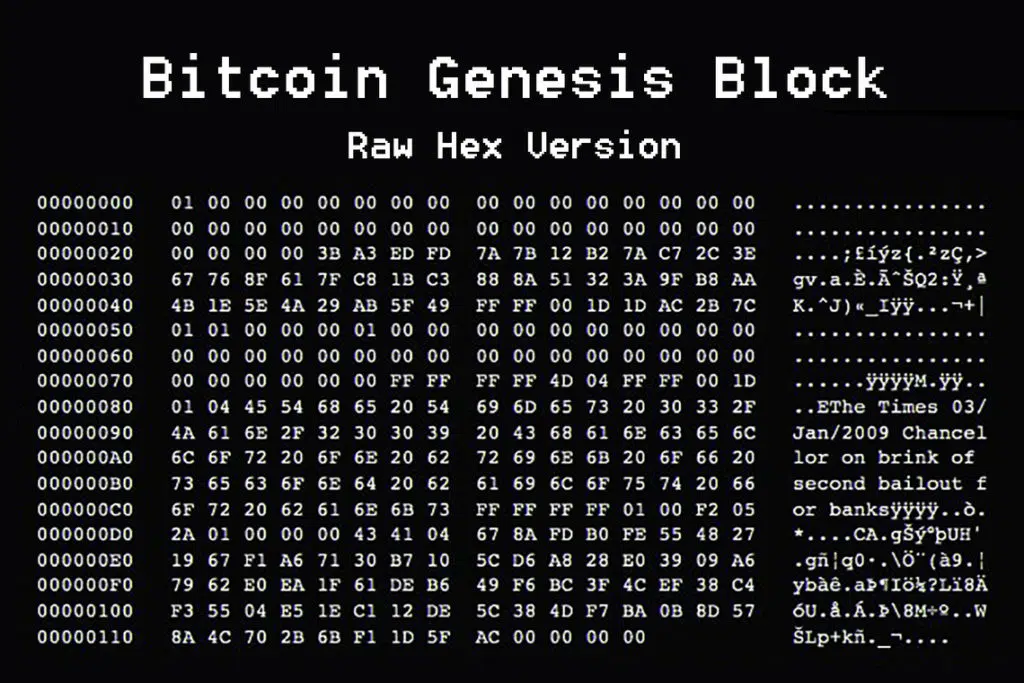
If you’re curious to know what it looked like, here’s the raw hex version of the Genesis Block:
A few months later, on October 12th 2009, Satoshi made the world’s first bitcoin transaction on the blockchain. He sent 10 BTC to his friend and supporter Hal Finney, a famous programmer who was among the first to download the software the day it was released, together with Wei Dai, the creator of B-Money we mentioned before.
That day was also the first time Bitcoin gained value. Martti Malmi, a Finnish developer, sold 5,050 BTC to NewLibertyStandard for $5.02 using PayPal. That means that back then 1 BTC was worth $0.0009.
Despite all the ups and downs, Bitcoin has remained the number one cryptocurrency for over a decade now. It has come far in terms of being accepted as a possible form of payment by billion-dollar companies and has gained interest from many of the world’s financial institutions.
Cryptocurrency Mining
In the same way in which gold has to be mined out of the ground, Bitcoin has to be digitally mined as well. The mining process takes place on the blockchain peer-to-peer network where every transaction reaches the users’ computers. In order to validate the transaction and mine the coins, these “miners” have to solve a complex mathematical problem by running a hash function.
The solution has to be accepted by other miners, and that’s when a transaction gets verified and added to the chain of data blocks. Since this requires a lot of time and computational power, miners receive cryptocurrencies as an award for their effort in maintaining the blockchain network. Bitcoin adds a new block to the blockchain every 10 minutes on average.
However, there’s a fixed supply limit of 21 million bitcoins that can be mined in total. When miners reach this number, the supply will be tapped out worldwide. No need to raise the alarm just yet because some experts have estimated that it will take more than one hundred years to mine that much bitcoins.
Cryptocurrency Properties
“When I first heard about Bitcoin, I thought it was impossible. How can you have a purely digital currency? Can’t I just copy your hard drive and have your bitcoins? I didn’t understand how that could be done, and then I looked into it and it was brilliant” – Jeff Garzik, CEO of Bloq Inc
So far, we’ve learned what cryptocurrencies are and how and why they came to be, but we’re pretty sure this has raised even more questions in your head than it has answered. Okay, digital coins are mined on the blockchain, and yes, they’re useful because they’re decentralized which equals privacy, lower transaction costs, and greater speed. But how is all this possible anyway?

Decentralization and Security
If blockchain technology had begun as a project owned by a certain company where that company would’ve been its central authority, the whole project and ideology behind it would’ve been dead in the water from the start. Instead, blockchain uses a network where anyone can take part in and be rewarded for their work, and have the option to join in or leave anytime they want. But most importantly, they will never be able to control the network.
So, if you want to send your friends some bitcoins that you’ve been keeping in your digital wallet, they’ll just need to have a wallet themselves and then you can send those coins much like you send a regular email. In order for the coins to arrive in your friend’s wallet, all of the people who have joined the network will have to agree that your transaction is valid. The bigger the number of people who do that, the more secure your transfer is. But how?
All these people work on their computers and compete on solving the algorithm that will make your transaction work. This requires computing power, advanced cryptography, and encoding. Once someone succeeds, they send the code to all the other computers working on it who, once they see the answer, can easily check it and confirm it. The transaction is verified, put in a record, and a copy remains on each participating computer.
This is a type of consensus method known as proof-of-work, where the mining community takes responsibility to protect the decentralized blockchain network from double-spending and forging coins. Moreover, if anyone tries to tamper and make changes to a stored record, their changes won’t match up with the logs on the participating computers and will be rejected. An attempt to gain control over all these computers will take an impossible amount of computing power.
Anonymity
One of the best things about cryptocurrency transactions is that they aren’t linked to real identities. However, if you were one of those who believed that cryptocurrencies are anonymous by design, we’ll have to disappoint you. Cryptocurrencies are actually pseudonymous. Your transaction is only linked to an electronic address which becomes your digital pseudonym. If no one knows your pseudonym, no one will find out when and how much crypto you are buying or selling. Your privacy is guaranteed if you keep your digital identity to yourself.
Transparency
The blockchain stores the history of all the transactions that have ever taken place on the network. This is what makes cryptocurrencies both private and public, or rather transparent. If a company uses the electronic address publicly, anyone can log online and check how much BTC or other cryptos it owns, and how frequently it makes any purchases with them. But if the company takes great care to keep its address internally safe, it can be tracked only with very sophisticated software.
This explains why companies often resort to unique electronic addresses for every new transaction to achieve complete privacy.
Speed
Another valuable property of cryptocurrencies is the speed at which you complete your money transfer. Unlike banking transfers and credit card transaction which might take up to several days, especially if more than one bank is involved (e.g. international transfers). Regardless of your place of residence and that of the person you’re sending money to, transfers happen instantaneously as long as you have a device to download and use the software on.
This is an advantage that makes cryptocurrencies even more relevant for the busy lifestyle that has become the norm today.
Portability
Fiat currencies have to be carried around in your pocket and presented physically when you want to purchase something. Of course, most of us use their debit or credit cards nowadays, but that also ties you to a third-party, namely, a bank. In comparison, cryptocurrencies can be transferred from one account to another or used as a payment method from every single gadget, including your smartphone regardless of the amount!
Transaction Fees
Third parties thrive on transaction fees and use every chance they get to rip you off. You’re charged for withdrawals and transfers, and the amount depends on whether the transactions are made in the same bank, to other banks in the country, or internationally (the last ones are the most expensive).
The mining of cryptocurrencies is a mathematical process which is why the commission fee in the Bitcoin blockchain system is lower than in any other. It equals 0.1% of the transaction amount and is rewarded to the miners for verifying the transaction.
Ownership
In every other cash system in the world, your account is owned by someone else besides you who has control over your money, and the job of an intermediary. If the company suspects your account of misuse, it can freeze all of your money without consulting you. It will take additional time for you to reassure them that you haven’t been engaged in any illegal activity and regain access to your funds.
This brings us to the best thing about cryptocurrencies and the electronic cash system they’re part of. You’re the only one in charge of your money! You own the private and public key that represents your electronic address. That’s why you should take extra care not to lose it or share it with untrusted parties.
The Benefits of Using Cryptocurrencies
Cryptocurrency skeptics seriously doubt that digital coins serve any additional functions to those already provided by the regular currencies. Apart from some more privacy, usually abused for illegal activities, they wonder what else makes digital assets valuable for consumers around the world.
The Advantages of Push-Based Payments
Traditional payment systems like credit cards and the ACH network are all pull-based systems. This means that even though the customers think they’re initiating the transaction themselves, in reality, they’re actually sending an instruction to their financial institution (e.g. their bank) to authorize the merchant to “pull” money from their account.
The advantages of this model are outweighed by the disadvantages. You’re required to place your trust not only in the merchant but also in the third-parties involved such as their IT supplier and bank, and your own card-issuer.
On the other hand, cryptocurrency payments are push-based. They reverse the transaction process by allowing customers to be in charge. They’re the ones who get the merchant’s account information and initiate the transaction, instructing their financial institution to “push” money out of their account. They don’t have to worry that the merchant will misuse their account information and continue to charge them without approval.

Source: CoinCenter
The Advantage of Micropayments
Before cryptocurrencies, electronic payments always came with an additional transaction cost deduced by third-party financial institutions for the service. Therefore, if you wanted to make a very small payment or money transfer, i.e. a micropayment, the transaction fee would be higher than the payment itself.
Paying with cryptocurrencies makes these micropayments viable and opens the door for a whole host of new business models. Take “The Geek’s Guide to Britain” for example, a travel guide published by The Register and sold for $25 in paperback. On a crypto platform, you can buy the same guide in digital format for about $3, or purchase only one chapter for $0.12, an amount that would be unviable with credit cards or on the ACH network.
Where To Buy Cryptocurrencies?
Cryptocurrency exchanges are online platforms where individuals can buy, sell, or trade cryptocurrencies. They act as intermediaries between buyers and sellers. These exchanges provide a convenient way for investors to access the global cryptocurrency market.
Trustworthiness and security are crucial considerations when choosing a cryptocurrency exchange. Some of the most popular cryptocurrency exchanges offer a wide range of features to facilitate trading. Additionally, exchanges typically charge fees for transactions, but differ in their fee structures. It is essential for investors to compare these fees and choose an exchange that best suits their needs.
Another important aspect of cryptocurrency exchanges is the level of liquidity they provide. Exchanges with higher liquidity offer more competitive prices and faster transaction times.
List of Cryptocurrency Exchanges A to Z
- Bancor Review
- BankCEX Review
- Binance Review
- bingX Review
- Bisq Review
- Bit2Me Review
- Bitbns Review
- Bitbuy Review
- Bitcoiva Review
- Bitfinex Review
- Bitflyer Review
- Bitget Review
- BitKan Review
- BitMart Review
- BitMEX Review
- BitOasis Review
- Bitpanda Review
- Bitso Review
- Bitstamp Review
- Bitvavo Review
- Blockchain.com Review
- BTC Markets Review
- BTCC Review
- BuyUcoin Review
- Bybit Review
- CEX.IO Review
- Changelly Review
- ChangeNOW Review
- Coinbase Review
- CoinDCX Review
- CoinEx Review
- Coinhako Review
- CoinJar Review
- CoinList Pro Review
- Coinmama Review
- Coinmetro Review
- Coinsbit Review
- CoinSmart Review
- CoinSpot Review
- Coinsquare Review
- Coinstash Review
- CoinSwitch Review
- Cointree Review
- CoinZoom Review
- Crypto.com Review
- CryptoPay Review
- CryptoSpend Review
- Curve Finance Review


